The Power of YubiKey: Strengthening Identity Security and Defeating Phishing Attacks
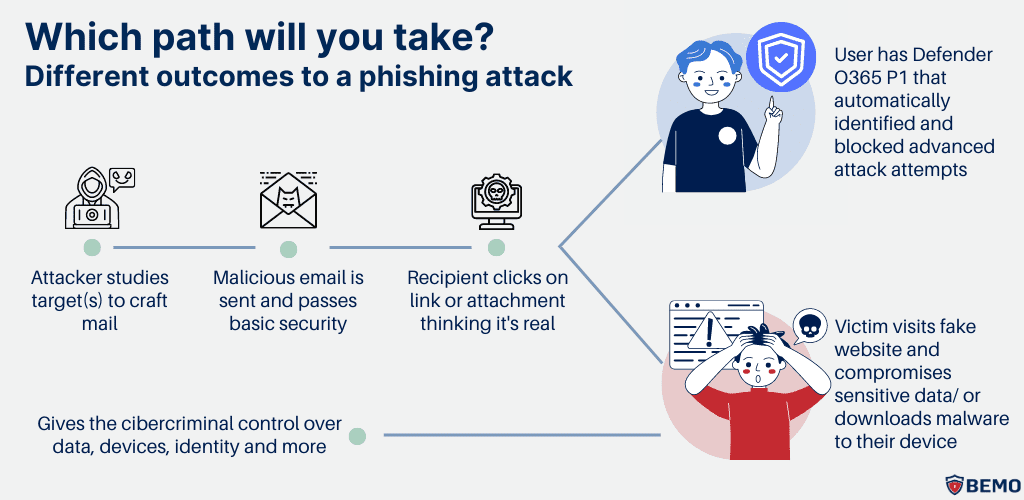
In an era where cyber-attacks are more sophisticated than ever, identity has become the new security perimeter. Passwords alone are no longer enough — and the growing wave of phishing, credential theft, and social-engineering attacks demands stronger, hardware-rooted defences.At KUKZY, we integrate intelligent identity-protection solutions that combine security, simplicity, and resilience. One of our most trusted technologies in this mission is the YubiKey — a small but powerful hardware security key that delivers enterprise-grade protection against account compromise. What Is a YubiKey? A YubiKey is a physical authentication device developed by Yubico. It supports multiple modern authentication protocols including: This small USB- or NFC-enabled key provides multi-factor authentication (MFA) and passwordless login to corporate systems, cloud platforms, and identity providers like Microsoft Entra ID (Azure AD), Google Workspace, Okta, Cisco Duo, and others. Why YubiKey Matters in Cybersecurity Hardware-Rooted Trust Unlike software-based MFA (SMS or authenticator apps), YubiKey performs cryptographic operations directly on the device — isolated from the operating system and potential malware. This creates a zero-trust anchor — an unforgeable identity signal that can’t be intercepted, cloned, or replayed. Phishing-Resistant Authentication Phishing remains one of the most successful cyber-attack vectors. Hackers lure users into fake login portals, capturing usernames and passwords.YubiKey prevents this by binding the authentication to the legitimate domain through public-key cryptography. Even if a user clicks a fake link, the YubiKey simply refuses to authenticate because the origin does not match the registered site. This is true phishing resistance, now endorsed by NIST SP 800-63B and the FIDO Alliance as the gold standard for authentication security. Passwordless and Frictionless Security By using FIDO2/WebAuthn, YubiKey enables users to log in without passwords entirely — combining: The result is stronger security with less user friction.At KUKZY, we integrate YubiKey within enterprise Single Sign-On (SSO) and Conditional Access frameworks to deliver seamless authentication across devices and cloud services. Compliance and Digital-Forensic Readiness For organisations operating under ISO/IEC 27001, NCSC Cyber Essentials Plus, or GDPR, implementing YubiKey supports: This reduces exposure to insider threats, credential abuse, and lateral movement attacks. Operational Simplicity YubiKey doesn’t rely on batteries, network connectivity, or mobile devices.It works across Windows, macOS, Linux, iOS, and Android, making it ideal for hybrid and high-security environments such as: At KUKZY, we deploy YubiKeys through Microsoft Intune, ensuring rapid enrolment, secure lifecycle management, and zero-touch provisioning for users. Technical Insight: How YubiKey Beats Phishing Every YubiKey registration generates a unique key pair: When you log in: Since the cryptographic challenge is domain-specific and non-reusable, even if attackers trick a user into entering credentials elsewhere, the YubiKey cannot be coerced into signing an illegitimate request. YubiKey in Action at KUKZY At KUKZY, we integrate YubiKey into our Digital Forensic Readiness Framework and Identity Access Management (IDAM) architecture.This ensures: Our rollout across departments has already demonstrated: Final Thoughts The journey toward a passwordless, phishing-resistant enterprise begins with identity assurance.YubiKey doesn’t just strengthen security — it simplifies it, transforming identity verification from a weak point into a core pillar of digital resilience. At KUKZY, we believe in “Securing Every Think, Protecting Every Thing”.By adopting YubiKey and other advanced zero-trust controls, we empower organisations to move beyond passwords and into a future where authentication is effortless, hardware-anchored, and unphishable.
How KUKZY APRM Enables Compliance With Global Cybersecurity & Data Protection Standards

A Unified Approach to Security, Visibility, and Forensic Readiness In today’s rapidly evolving cyber landscape, organisations face increasing pressure to demonstrate continuous compliance, maintain strong audit trails, and implement robust security controls that meet global regulatory standards. Traditional compliance models often rely on periodic checks and manual assessments — an approach that leaves dangerous gaps in visibility and exposes organisations to costly breaches and non-compliance penalties. To solve this, KUKZY developed the Automated Proactive Readiness Model (APRM) — a next-generation security and forensic readiness framework engineered to deliver real-time monitoring, continuous assurance, and automated alignment with compliance requirements. APRM integrates security, infrastructure, and forensic intelligence into a single unified model, helping organisations meet the technical, operational, and audit requirements of globally recognised security frameworks. This blog explores how KUKZY APRM supports compliance with: 1. How KUKZY APRM Supports PCI DSS Compliance PCI DSS requires organisations handling cardholder data to implement strong access controls, protect data, maintain secure systems, and monitor all activities related to cardholder data environments. KUKZY APRM enables PCI DSS readiness by providing: Continuous Log Monitoring & Centralised Visibility Every user action, system change, and network event is captured, correlated, and stored — supporting PCI Requirement 10 (Track and monitor all access). File Integrity Monitoring (FIM) Detects unauthorised modifications to critical files, configurations, and payment-processing systems (PCI Requirement 11.5). Vulnerability Detection & Patch Monitoring APRM identifies vulnerabilities, outdated software, and weak configurations that may violate PCI Requirements 6.1 and 6.2. Audit-Ready Reporting Automated reports demonstrate compliance during PCI audits and assessments. Identity & MFA Integration Supports PCI Requirement 8 with strong authentication controls and integration with YubiKey, SSO, and PAM systems. Outcome: Organisations achieve stronger protection of cardholder data, reduced fraud exposure, and faster certification processes. 2. How KUKZY APRM Supports ISO/IEC 27001 (ISMS) Compliance ISO/IEC 27001 mandates the implementation of an Information Security Management System (ISMS) covering risk management, operational controls, monitoring, and incident response. KUKZY APRM strengthens ISO 27001 compliance through: Risk-Based Monitoring APRM continuously assesses risks across endpoints, servers, cloud workloads, and networks — supporting ISO 27001 Clause 6 (Planning and Risk Management). Controls Mapping to Annexe A APRM provides real-time enforcement and monitoring of controls such as: Incident Detection & Forensic Analysis With built-in forensic readiness, APRM helps organisations meet ISO 27035/27043-aligned incident handling requirements. Audit Logging & Retention Supports A.12.4 by enabling detailed audit trails across all systems. Automated Evidence Collection Ensures compliance documentation is accurate, complete, and always up to date. Outcome: Organisations can establish and maintain a fully monitored, evidence-backed ISMS with minimal manual effort. 3. How KUKZY APRM Supports HIPAA Compliance HIPAA (Health Insurance Portability and Accountability Act) mandates strict controls to protect electronic protected health information (ePHI). Healthcare providers, insurers, and partners must secure access, monitor activities, and detect suspicious behaviour. KUKZY APRM supports HIPAA Security Rule requirements (164.308, 164.310, 164.312, 164.316) through: Access Monitoring & Authentication Controls Tracks logon attempts, access to sensitive databases, and ePHI system activities — supporting Technical Safeguards. Integrity Monitoring Detects and alerts on unauthorised changes to patient records, applications, or medical systems. Audit Controls & Activity Logging Comprehensive logs meet HIPAA’s requirement to record all activity related to ePHI systems. Transmission & Endpoint Security APRM identifies insecure configurations, weak encryption, and unauthorised communications. Incident Response & Documentation Provides forensic evidence for HIPAA breach investigations and reporting obligations. Outcome: Healthcare organisations significantly reduce the risk of ePHI breaches and strengthen compliance with administrative, physical, and technical safeguards. 4. How KUKZY APRM Supports NIST SP 800-53 Compliance NIST SP 800-53 defines a comprehensive set of security and privacy controls for federal agencies, defence sectors, and highly regulated industries. KUKZY APRM maps to key control families, including: AC — Access Control Continuous validation of user permissions, MFA, login behaviours, and session activity. AU — Audit & Accountability APRM automates audit logs, event correlation, and long-term retention for accountability. CM — Configuration Management Monitors secure configurations and detects deviations from baseline. IR — Incident Response Supports detection, triage, analysis, and evidence preservation for all incidents. SI — System & Information Integrity Threat detection, malware visibility, vulnerability assessment, and health monitoring. RA — Risk Assessment Real-time collection of asset, vulnerability, and event data supports continuous risk evaluation. Outcome: Organisations achieve a strong, federal-aligned security posture suitable for government, defence, and high-assurance industries. Unified Compliance Through KUKZY APRM Unlike traditional compliance tools that operate in silos, KUKZY APRM brings together: This unified model ensures that organisations are not only compliant — but proactively protected, forensically prepared, and operationally resilient. APRM transforms compliance from a checklist into a continuous, automated process. It gives organisations a living, breathing security posture that adapts to threats, supports audits, and strengthens overall cyber defence. Final Thoughts In a world where cybersecurity risk is constant and regulatory requirements are intensifying, organisations need more than static security controls. They need a model that is: The KUKZY Automated Proactive Readiness Model (APRM) delivers precisely that. By aligning with global frameworks such as PCI DSS, ISO/IEC 27001, HIPAA, and NIST SP 800-53, KUKZY empowers organisations to meet compliance mandates with ease while enhancing their ability to detect, respond to, and recover from cyber incidents.